 I do not usually turn to BuzzFeed as a source of eDiscovery learning, but I was interested to see a post about pictures posted to his Instagram account by a Russian soldier apparently operating in Ukraine. Its title Does This Soldier’s Instagram Account Prove Russia Is Covertly Operating In Ukraine? is slightly misleading – there is nothing “covert” about blasting your GPS information out into the Internet, though it appears that the soldier was unaware that he was doing that. Or indifferent about it. Or stupid. Or all of these things.
I do not usually turn to BuzzFeed as a source of eDiscovery learning, but I was interested to see a post about pictures posted to his Instagram account by a Russian soldier apparently operating in Ukraine. Its title Does This Soldier’s Instagram Account Prove Russia Is Covertly Operating In Ukraine? is slightly misleading – there is nothing “covert” about blasting your GPS information out into the Internet, though it appears that the soldier was unaware that he was doing that. Or indifferent about it. Or stupid. Or all of these things.
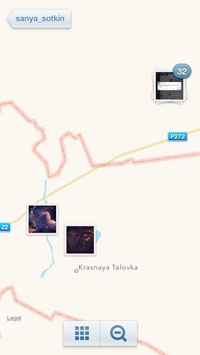
The picture here, incidentally, from the BuzzFeed page, shows the Ukraine-Russia border (the red lines) both above and below the apparent site of the pictures – this is a narrow part of Ukraine sticking eastwards into Russia.
However bullish Putin may be about the presence of his troops in Ukraine, it is unlikely that he will be thrilled to see that one of his soldiers has (presumably inadvertently) produced evidence which simultaneously shows him manning a missile launcher system and pins him to a location in Ukraine. Quite apart from matters of international comity (or at least the illusion of it), it is a weapon of this kind, from somewhere near this place, which blasted Malaysian Airlines Flight 17 out of the sky killing 298 people, including a large number of children.
That kind of crime outstrips any civil or criminal activity you can think of, but there are lessons here for more mundane offences. The eDiscovery lesson, in case that is not clear, is that all sorts of everyday devices capture, retain and publish evidence of time and place.
 Apart from being a good illustration of something I bang on about a lot, it ties in with two other things I have seen this week. One is an article on Inside Counsel by David Freskos and Bryan Lee of FTI Technology called Using smart phone location services to help solve investigations.
Apart from being a good illustration of something I bang on about a lot, it ties in with two other things I have seen this week. One is an article on Inside Counsel by David Freskos and Bryan Lee of FTI Technology called Using smart phone location services to help solve investigations.
It opens with a story of a defecting employee whose photographs of his former employer’s manufacturing plant carried GPS coordinates which were easily traced on Google Earth.
The article goes on to make suggestions both for investigators who may rely on such information (if they only remember to look for it) and on corporate policies about the use of such devices.
 The second is the product description page for AccessData’s Mobile Phone Examiner PLUS which is in my recent electronic reading pile thanks to a recent tweet from AccessData which emphasises the ease and speed with which MPE+ supports eDiscovery with visualisation tools allowing you to see communication relationships among contacts and graphical data timelines. That page also has a link to an AccessData white paper called The Future of Mobile E-Discovery.
The second is the product description page for AccessData’s Mobile Phone Examiner PLUS which is in my recent electronic reading pile thanks to a recent tweet from AccessData which emphasises the ease and speed with which MPE+ supports eDiscovery with visualisation tools allowing you to see communication relationships among contacts and graphical data timelines. That page also has a link to an AccessData white paper called The Future of Mobile E-Discovery.
The third is a demonstration I saw this week of real-time collection of social media information – not just historic tweets or Facebook entries but those which are happening in real time. For myself, I don’t care who knows where I am and I am probably tweeting about it anyway. If you are spying on your employers’ warehouse or working on missile launches in occupied territory then you may have cause for concern.
Lawyers engaged in eDiscovery may think of this both positively and negatively – on the one hand, this is evidence which may make or break a case or, at least, bolster or undermine assertions made by a witness as to his or her activities. More negatively, it may be negligence or breach of duty to overlook the possibility of such data existing.
My thanks to tweeter @PME2014 for the pointer to the Ukraine article.

